A Complete Guide to the CMMC Framework
Anticipated for completion by the end of 2023, the Department of Defense (DOD) is set to finalize a transformative update to the Cybersecurity Maturity Model Certification (CMMC) framework and associated cybersecurity standards for defense contractors. Initially introduced through an advance notice of proposed rulemaking in November 2021, this upcoming regulation, known as CMMC 2.0, is poised for finalization within the specified timeframe. CMMC, a standardized cybersecurity protocol mandated by the DOD, uniformly implements cybersecurity controls across the entire DOD supply chain.
This framework categorizes contractors into five ascending levels of cybersecurity maturity, ranging from “basic” to “advanced,” with the primary aim of safeguarding sensitive unclassified information shared between the DOD and its contractors. Contractors seeking contracts with CMMC compliance requirements must align their security measures with the specified level mandated by the respective contract.
What Is the Cybersecurity Maturity Model Certification?
Efforts to develop the CMMC were spearheaded by the Office of the Under Secretary of Defense for Acquisition and Sustainment, sometimes called the OUSD(A&S).
This office has partnered with key DoD stakeholders, federally funded research and development centers, university-affiliated research centers, and corporations within the defense industrial base.
Together, they created a unified standard that is meant to serve as a guide for implementing cybersecurity protocols. These standards apply not only to the DoD directly but also to the more than 300,000 companies that make up the DIB supply chain.
The maturity model was developed in response to the surge in cyber threats that are being directed at DoD contractors.
The first iteration of the CMMC was released on January 31, 2020. Since then, the OUSD(A&S) has released two major updates. The old version is known as the CMMC Model v1.02. The updated CMMC 2.0 introduces a streamlined three-level model, replacing the previous five-tier system in CMMC 1.02. Unveiled on July 17, 2021, the three CMMC levels consist of Level 1 (Foundational), Level 2 (Advanced), and Level 3 (Expert). Assessment requirements for CMMC vary depending on the desired certification level.
What the CMMC Means for DoD Contractors
Before the release of the CMMC, each contractor was responsible for developing and monitoring the security of their IT resources. This included safeguarding any DoD data that was being stored or transmitted on their networks.
The result? Massive inconsistencies in cybersecurity practices among the several hundred thousand companies involved in the DIB supply chain.
DoD contractors must begin reviewing the CMMC’s requirements immediately, as deployment of this certification system has already started. Compliance with the Cybersecurity Maturity Model Certification will be included in future DoD contracts. Each company will have to pass a third-party assessment in accordance with their designated CMMC level.
The first step DoD contractors need to do, if they haven’t already, is to complete a NIST 800-171 Self-Assessment and upload the score to the Supplier Performance Risk System (SPRS) website. The Defense Federal Acquisition Regulation Supplement (DFARS) is referenced in nearly all DoD contracts and specifies cybersecurity standards that are required by law.
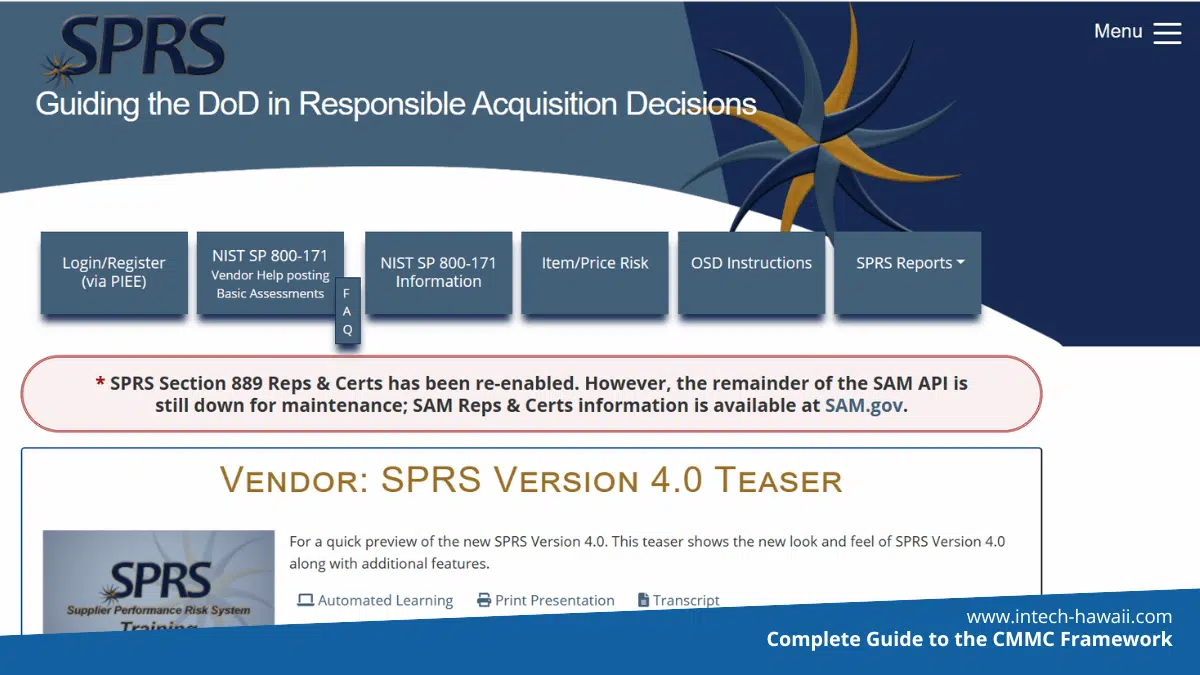
SPRS Website
Since 2017, the DFARS 252.204-7012 clause has required defense contractors to implement the 110 cybersecurity controls defined in NIST 800-171 to protect Controlled Unclassified Information (CUI). But the big change came November 30, 2020 when the DFARS NIST 800-171 Interim Rule was put in place that requires contractors to perform the Self-Assessment.
In addition to the Self-Assessment and Score, contractors are required to generate some documentation to validate compliance. This includes a System Security Plan (SSP) showing currently implemented controls and a Plan of Action & Milestones (POA&M) for controls not fully implemented. Some written policies and procedures are also required to validate that these controls are implemented.
Contractors that start self-assessing and identifying weaknesses in their current cybersecurity protocols will be better prepared for the CMMC certification process. The OUSD(A&S) webpage includes assessment guides for contractors so that they will know which criteria they will be graded on.
Why Was the CMMC Introduced?
The Cybersecurity Maturity Model Certification was introduced to address several key issues, which include the following:
An Uptick in State-Sponsored Hacking
In just the last few years, there has been a massive uptick in state-sponsored hacking. Companies within the DoD supply chain have been the target of cybercrimes that were instigated by industry competitors, international criminals, and foreign nations.
A few of the countries that pose the greatest threat to the DIB include Iran, Russia, North Korea, and China.
Like every other developed nation, the U.S.’s military is outfitted with advanced technological assets. This makes their supply chain especially vulnerable to cybersecurity threats. The CMMC is designed to protect essential weapon systems throughout their entire life cycles.
Inconsistent Cybersecurity Practices by Subcontractors
Subcontractors were identified as the most vulnerable component of the DIB supply chain. The DoD’s tier-one contractors generally have multimillion-dollar cybersecurity budgets. They are also closely regulated. Conversely, subcontractors are loosely monitored and held to much less stringent standards.
Since a large portion of the defense industrial base consists of small and medium-sized suppliers, this lack of regulation has left the DoD open to cyberattacks.
CMMC regulations are being applied universally. This ensures that any company involved in the DoD supply chain meets the minimum security standards.
A Need to Shift Corporate Culture
Unfortunately, many smaller DoD defense suppliers do not view themselves as likely targets for cybercriminals. This lax approach towards cybersecurity is ingrained in the culture of the DIB supply chain.
One of the primary goals of the CMMC is to facilitate a cultural shift that will change the entire defense contractor industry.
The CMMC will be incorporated directly into defense contractor agreements. Failing to comply with the regulations outlined in the CMMC will result in stiff penalties. Violators could have their current contracts voided and will lose out on future opportunities with the DoD.
Laying the Framework for Improved Cybersecurity
The CMMC functions in a “maturity model” format. It is divided into three progressive certification levels.
The latest iteration of the CMMC framework comprises three increasingly sophisticated tiers: (1) Foundational, (2) Advanced, and (3) Expert. At each level, contractors must comply with a set of security controls and either demonstrate compliance autonomously or undergo triennial certification through a third-party or government-led assessment.
What are the 3 Levels of CMMC 2.0?
Each CMMC level mandates that contractors adhere to a specific set of security controls and demonstrate compliance.
In certain instances, the Department of Defense permits uncertified contractors to employ a Plan of Actions & Milestones (POAM) to show their commitment to achieving certification by a designated date. In even rarer cases, contractors may request a waiver for all requirements. Comprehensive details regarding POAMs and waivers have not been released by the DoD.
CMMC Level 1: Foundational
Contractors dealing with FCI must meet Level 1 CMMC compliance, aligning with the 17 basic cyber hygiene practices outlined in Federal Acquisition Regulation (FAR) 52.204.21 and further defined in NIST SP 800-171.
As FCI is not classified as sensitive information, Level 1 contractors are allowed to self-assess their cybersecurity. Annual submission of scores and documentation to the Supplier Performance Risk Systems (SPRS) is mandatory. Third-party or government-led assessments are not required for Level 1 compliance.
CMMC Level 2: Advanced
Contractors managing CUI are obligated to achieve Level 2 CMMC compliance, incorporating the initial 17 Level 1 practices and an additional 93 practices from NIST 800-171. Similar to Level 1, the DoD mandates annual cybersecurity assessments with score and documentation submission to SPRS.
For “prioritized acquisitions,” Level 2 contractors must undergo certification by a CMMC Third-Party Assessment Organization (C3PAO) every three years. The Cyber Accreditation Body (AB) introduced the CMMC Assessment Process (CAP) to guide Level 2 contractors in preparing for their assessment.
CMMC Level 3: Expert
Contractors handling the most sensitive CUI must attain Level 3 CMMC compliance, aligning with all 110 NIST 800-171 controls and an additional set of controls (yet to be specified) from NIST 800-172.
Unlike Levels 1 and 2, Level 3 compliance requires contractors to undergo certification through a government-led assessment. As of February 2023, detailed information on the enhanced security requirements for this level has not been released by the DoD.
CMMC Compliance
The Cybersecurity Maturity Model Certification’s five maturity levels are further divided into 17 domains. These domains include a total of 43 capabilities. Some domains include a single capability, while some incorporate as many as five different aptitudes. Not all domain capabilities are required for each level of CMMC.
According to theNational Institute of Standards and Technology, a capability can be defined as “a set of mutually reinforcing security controls implemented by technical, physical, and procedural means.” These controls are generally selected with the goal of achieving specific information security-related outcomes.
The 17 domains and 43 capabilities are as follows:
Access Control
Access control is the cybersecurity principle of regulating what or who can view certain resources within a network. The CMMC has allocated 4 essential capabilities under this domain.
In order to be in compliance, contractors must:
- Establish system access requirements
- Control remote system access
- Control internal access
- Limit access to authorized individuals
Access control is one of the most basic components of cybersecurity, which is why the CMMC places such emphasis on it during the assessment process.
Asset Management
Asset management or IAM (identity and asset management) focuses on managing digital identities of authorized users. This domain encompasses all policies, technologies, and programs that are designed to reduce access risks within a network.
The CMMC requires contractors to identify and document assets in order to comply with this capability domain.
Audit and Accountability
Also known as AU, the audit and accountability domain is designed to ensure that a contractor has sufficient controls in place. These controls are designed to provide evidence for system transactions so that they can be audited.
The AU process allows administrators to trace back and recover data in the event of a system failure, breach, or other incidents.
The four capabilities of the AU domain include defining audit requirements, performing regular auditing, identifying and protecting audit-related data, and reviewing and managing logs. Again, not all of these capabilities are required for all levels of CMMC.
Awareness and Training
Awareness and training are essential to changing the culture within a company. As the name suggests, the “awareness and training” domain is geared towards improving staff awareness of cybersecurity threats. This program also focuses on training those employees on how to identify and safeguard against these dangers.
The AT domain includes two capabilities, which are as follows:
- Actively improving security awareness
- Conducting regular training
A well-designed AT program is one of the best ways of protecting a company’s valuable data while also helping them to adhere to CMMC standards.
Configuration and Management
Configuration management (CM) is the domain that focuses on maintaining consistency within an organization. Configuration management utilizes automation to allow teams to build out systems more rapidly. It is also essential for auditing purposes, as it allows companies to track when changes occur within their network.
The CMMC identifies two capabilities that fall under the umbrella of CM. Contractors being assessed on this domain must establish configuration baselines and perform configuration and change management.
Identification and Authentication
The identification and authentication domain addresses concerns about unverified entities gaining access to a contractor’s network. This domain includes only one capability: Contractors must deploy an authentication process that grants access to authorized entities only.
Incident Response
The most comprehensive domain included in the CMMC is incident response. This domain contains five total capabilities, which contractors must demonstrate in order to obtain certification. These capabilities are focused on detecting and responding to cybersecurity incidents.
The five capabilities within this domain are as follows:
- Planning an incident response protocol
- Detecting and reporting cybersecurity incidents
- Developing a threat response to confirmed incidents
- Deploying a post-incident review process
- Testing the incident response protocol?
By including such a robust IR domain, the CMMC framework ensures that top-tier contractors have adequate cybersecurity protocols in place in the event of a breach.
Maintenance
Maintenance of their network is one of the most basic requirements set forth by the CMMC. This domain capability is included in every certification level.
While one would expect that DoD contractors already do this, there were concerns that smaller defense suppliers were neglecting to properly maintain their IT resources. Managed services for IT support is an option for smaller defense suppliers.
Media Protection
The “media protection” domain highlights key aspects of the General Services Administration’s IT Security Procedural Guide: Media Protection. The GSA states that media protection includes three integral elements, while the CMMC domain lists four capabilities. These are as follows:
- Identifying and marking media files
- Protecting said media
- Sanitizing media files
- Protecting media during transfers
Media protection capabilities must be designed to control access to any media related to CUI or other DoD contract data.
Personnel Security
As noted above, subcontractor security protocols were one of the DoD’s major concerns during the creation of the CMMC. It only stands to reason that personnel security is one of its seventeen designated domains. This domain includes two capabilities.
Contractors must develop and utilize a screening process for their personnel. In addition, they have to proactively protect CUI while personnel are interacting with said data. Failure to do so during precertification can result in a failed assessment while violations that occur post-contract can cause the agreement to be voided.
Physical Protection
Physical protection protocols are one of the most often overlooked aspects of cybersecurity. The CMMC wants to remedy the issue by assessing contractors’ current security practices. These companies must restrict physical access to key resources such as servers, computers, and other IT equipment.
Recovery
While most of the CMMC domains are directed at preventing data breaches, the “Recovery” capability focuses on overcoming a successful cyberattack.
Companies being assessed on this domain capability must have data back-ups. The specific backup requirements can be found in the assessment guide.
Risk Management
Risk management strategies are integral to improving cybersecurity across the defense industrial base supply chain. As a result, the CMMC assesses contractors on their risk management protocols.
To meet the minimum standards, companies must have protocols in place to identify and evaluate cyber threats. They must also develop a plan to proactively manage those risk factors.
Security Assessment
Also referred to as CA, the security assessment domain includes three capabilities. They are as follows:
- Developing a security plan
- Defining and managing controls
- Performing routine code reviews
Regular security assessments will help contractors identify shortcomings in their systems that may be exploited by cybercriminals.
Situational Awareness
Active threat monitoring capabilities are included in the “situational awareness” domain. Contractors are required to deploy threat monitoring technologies that search for potential dangers. Many of these technologies leverage machine learning and AI capabilities
Systems and Communications Protection
The SC or “systems and communications protection” domain contains two capabilities. The CMMC framework requires contractors to define the security requirements for their systems and communication resources. They must also control communications assets at system boundaries.
System and Information Integrity
The last of the 17 domains is “system and information integrity.” This domain includes the final four capabilities outlined by the CMMC.
Contractors that are being assessed for adherence to this domain must:
- Identify and manage information system shortcomings
- Perform routine system and network monitoring
- Actively identify malicious data
- Implement an advanced email protection protocol
The SI domain focuses on maintaining the sanctity of a contractor’s network. When used in conjunction with the other 16 domains, this set of capabilities can help contractors improve cybersecurity protocols.
Who Does the CMMC Apply to?
Fulfilling CMMC compliance is essential for DoD prime contractors, subcontractors, and suppliers within the DoD supply chain, ensuring eligibility for contract retention and acquisition. The DoD emphasizes that these requirements will have a widespread impact, affecting a substantial network of over 300,000 organizations.
When will the CMMC rulemaking be finalized?
Despite the Pentagon’s initial announcement nearly four years ago about certifying DoD contractors starting in 2020, implementing the program has proven to be intricate.
The anticipated final rule is scheduled to become effective in May 2023.
Although subject to potential changes, contractors are advised to proactively initiate steps towards CMMC compliance.
How to Prepare for the CMMC
Fortunately for DoD contractors and subcontractors, the OUSD (A&S) has provided them with plenty of information about the Cybersecurity Maturity Model Certification framework.
With that being said, we wanted to identify several ways that affected companies can start preparing for this landmark certification process.
Defense suppliers should:
Start Refining Current Cybersecurity Practices
While the OUSD (A&S) has not yet established any concrete accreditation procedures, contractors must start preparing for certification. Due to the vastness of the DIB, accreditors are likely to receive a flood of assessment requests. This will create a backlog that could delay the rollout of the CMMC program.
Companies that plan ahead and refine their cybersecurity practices could capitalize during the transition process. They may be able to obtain certification more quickly, thereby gaining the opportunity to respond to RFPs and earn lucrative contracts.
The top-tier contractors should also reach out to their preferred subcontractors. They should assist these entities with refining their own cybersecurity protocols. If these subcontractors fail to meet CMMC requirements, then those larger suppliers can no longer rely on their services.
Review RFPs and RFIs
As noted above, the DoD started including CMMC level requirements on some RFIs as early as 2020.
While they are not stringently enforcing all of these domain capabilities yet, contractors should start reviewing these RFPs and RFIs. By doing so, they can gain a better understanding of the CMMC level required for the services that they traditionally provide.
Contractors can determine what changes they will need to make to their cybersecurity protocols in order to be eligible for future contracts of similar scope.
In addition to reviewing RFPs, defense suppliers should actively engage with the Department of Defense and other agencies. This will allow them to glean additional insights about the CMMC framework and the certification process.
Review the Assessments on the OUSD Website
The assessment guides that the OUSD (A&S) published on their website are invaluable resources for defense contractors. These guides break down each domain and capability in great detail, which means that contractors can all but guarantee a passing review during the assessment process.
The assessment guides should be thoroughly reviewed prior to implementing changes to current cybersecurity protocols. This will help contractors avoid making unnecessary and potentially expensive alterations to their existing practices.
It is vital that DoD contractors make every effort to meet assessment requirements. A negative assessment will limit which RFPs that a contractor can respond to. In turn, this could negatively impact brand reputation and profitability.
Be Flexible
As a maturity-based framework, the CMMC will likely be amended to include new cybersecurity best practices.
Once a contractor has obtained the certification level required for DoD contracts, it does not mean that they can rest on their laurels. Instead, they must remain flexible so that they can respond appropriately to new requirements and maintain an optimal level of data security.
The CMMC has the potential to change the entire landscape of the defense industrial base and the thousands of companies that it includes. It is also positioned to become a valuable resource to defense suppliers, as it provides a detailed roadmap to improving cybersecurity protocols. Contractors that take full advantage of this assessment framework will be ideally positioned to compete in an ever-evolving industry.
If you need any assitance with your CMMC compliance, we can help you!